INFORMATION SECURITY
CONTINUTITY, RESILIENCE AND RECOVERY
ARTIFICIAL INTELLIGENCE
Security, Risk and Compliance (GRC)
Assessment & Assurance
Threat Protection
INFORMATION SECURITY
CONTINUTITY, RESILIENCE AND RECOVERY
ARTIFICIAL INTELLIGENCE
Security, Risk and Compliance (GRC)
Assessment & Assurance
Threat Protection


ISO/IEC 27001 Information Security Management System – Training Courses
About Course
Learn how to build your expertise in ISO/IEC 27001, the international standard for Information Security Management Systems (ISMS). Whether you're starting your journey or advancing your career, our ISO/IEC 27001 training courses and certifications equip you with practical, in-demand skills to protect data, manage information risks, and enhance digital trust.
What is ISO/IEC 27001?
Why is ISO/IEC 27001 important?
Certified ISO/IEC 27001 individuals will prove that they possess the necessary expertise to support organizations implement information security policies and procedures tailored to the organization’s needs and promote continual improvement of the management system and organizations operations.
Moreover, you will be able to demonstrate that you have the necessary skills to support the process of integrating the information security management system into the organization’s processes and ensure that the intended outcomes are achieved.
What Is ISO/IEC 27002?
ISO/IEC 27002 is an international standard that provides guidelines for selecting and implementing information security controls and for implementing information security standards and practices. It is applicable to organizations of all industries or sizes. ISO/IEC 27002 can be used to develop information security management guidelines tailored to the specific context of an organization.
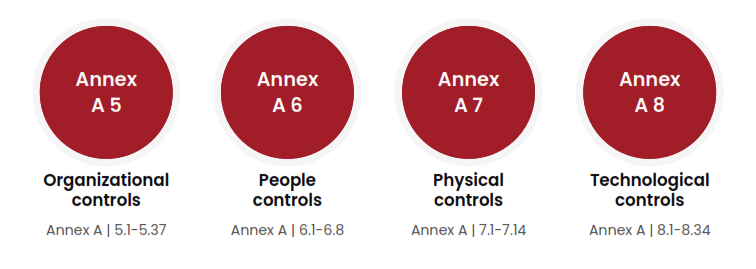
Originally published in 2005 and then updated in 2013, ISO/IEC 27002 was again revised and published in 2022. This new version provides a list of information security controls generally practiced in the information security industry, along with guidelines for their implementation. ISO/IEC 27002 provides four categories of information security controls: organizational (clause 5), people (clause 6), physical (clause 7), and technological (clause 8).
Why is ISO/IEC 27002 important for you?
An ISO/IEC 27002 training course provides guidelines for implementing, managing, and continually improving information security management in an organization.
Different organizations have different information security needs and capabilities. With that in mind, the controls of ISO/IEC 27002 are designed to be generic and flexible. The PECB ISO/IEC 27002 training courses are focused on equipping participants with the necessary knowledge for selecting, implementing, and managing such controls.
A PECB certification demonstrates the holder’s knowledge and ability to manage information security risks by applying relevant information security controls. It is also proof of their ability to help organizations preserve the confidentiality, integrity, and availability of information, protect against threats and vulnerabilities, and reduce information security risks. Certified ISO/IEC 27002 individuals can be crucial members of an ISMS implementation team.
PECB ISO/IEC 27002 certification benefits
A PECB ISO/IEC 27002 certificate will prove that you have:
- Understood the implementation of information security controls and control policies based on ISO/IEC 27002 guidelines
- Obtained practical knowledge of the approaches and techniques used for the implementation and effective management of information security controls
- Obtained the necessary expertise to support an organization in planning, implementing, and managing information security controls
- Understood risk management and its importance in determining appropriate information security controls
- Gained the ability to support organizations in continually improving their information security management system

ISO/IEC 27002 Benefits
How do I get started with ISO/IEC 27002 training?
PECB experts are more than willing to help you with the certification process and obtaining a PECB Certified ISO/IEC 27002 credential.
Contact us to begin with the first step.
Why choose PECB for ISO/IEC 27002 certification?
Certification is one of the key methods of demonstrating your competence and abilities. PECB certifications in information security are internationally recognized and accredited by top relevant authorities. PECB ISO/IEC 27002 certifications are a combination of extensive training and a comprehensive certification process, providing you professional credibility and boosting your opportunities for a successful career in one of the world’s fastest-growing and most in-demand industries.
PECB Certified ISO/IEC 27002 training courses available
Learn more about information security controls by attending the PECB ISO/IEC 27002 training courses. Below you can find the training that best suits you.
ISO/IEC 27001 Requirements and Controls?
Key Requirements of ISO/IEC 27001
ISO/IEC 27001 outlines several mandatory requirements that ensure a systematic approach to managing sensistive information. The most important rrequirements include:
- Context of the Organization
- Identify internal and external issues affecting information security.
- Determine the needs and expectations of stakeholders.
- Leadership and Commitment
- Top management must demonstrate active involvement in ISMS implementation.
- Establish clear roles, responsibilities, and policies.
- Risk Assessment and Risk Treatment
- Identify, analyze, and evaluate risks to information security.
- Implement appropriate risk treatments to mitigate identified risks.
- Support
- Provide adequate resources, training, and communication to ensure ISMS effectiveness.
- Operation
- Plan, implement, and control ISMS processes.
- Manage risks and security incidents effectively.
- Performance Evaluation
- Conduct internal audits and management reviews to evaluate ISMS performance.
- Continual Improvement
ISO/IEC 27001 Annex A Controls
ISO/IEC 27001 was updated in 2022 to ensure that information security management systems based on it effectively address the ever-evolving security challenges. The revision mainly focused on Annex A, where its controls were restructured into four themes, and the number was reduced from 114 to 93 controls.
The four themes of the security controls of ISO/IEC 27001:2022 are:
- Organizational Controls
- Information Security Policies: Develop and implement comprehensive security policies.
- Incident Management: Have processes in place for reporting and responding to security incidents.
- People Controls
- Awareness and Training: Ensure employees understand security risks and practices
- Screening: Conduct background checks during recruitment.
- Physical Controls
- Secure Areas: Protect physical access to information processing facilities.
- Equipment Security: Prevent loss or damage to assets.
- Technological Controls
- Access Control: Restrict system access based on roles and responsibilities.
- Cryptography: Use encryption to protect sensitive data.
The main changes between ISO/IEC 27001:2013 and ISO/IEC 27001:2022
The transition from ISO/IEC 27001:2013 to ISO/IEC 27001:2022 introduces significant updates to align with evolving cybersecurity and privacy needs. The standard title has expanded from focusing solely on “information security management systems” to incorporating “information security, cybersecurity, and privacy protection” in the 2022 version. Technical revisions include replacing terms such as “international standard” with “document” and “may” with “can,” reflecting a more flexible and modern approach.
Related Courses
- Country: Canada
- Location: Worldwide Virtual Online - Live / E-Learning
- Language: English
- Country: Canada
- Location: Worldwide Virtual Online - Live / E-Learning
- Language: English
- Country: Canada
- Location: Worldwide Virtual Online - Live / E-Learning
- Language: English
- Country: Canada
- Location: Worldwide Virtual Online - Live / E-Learning
- Language: English

